Digital Trust Is Critical Infrastructure
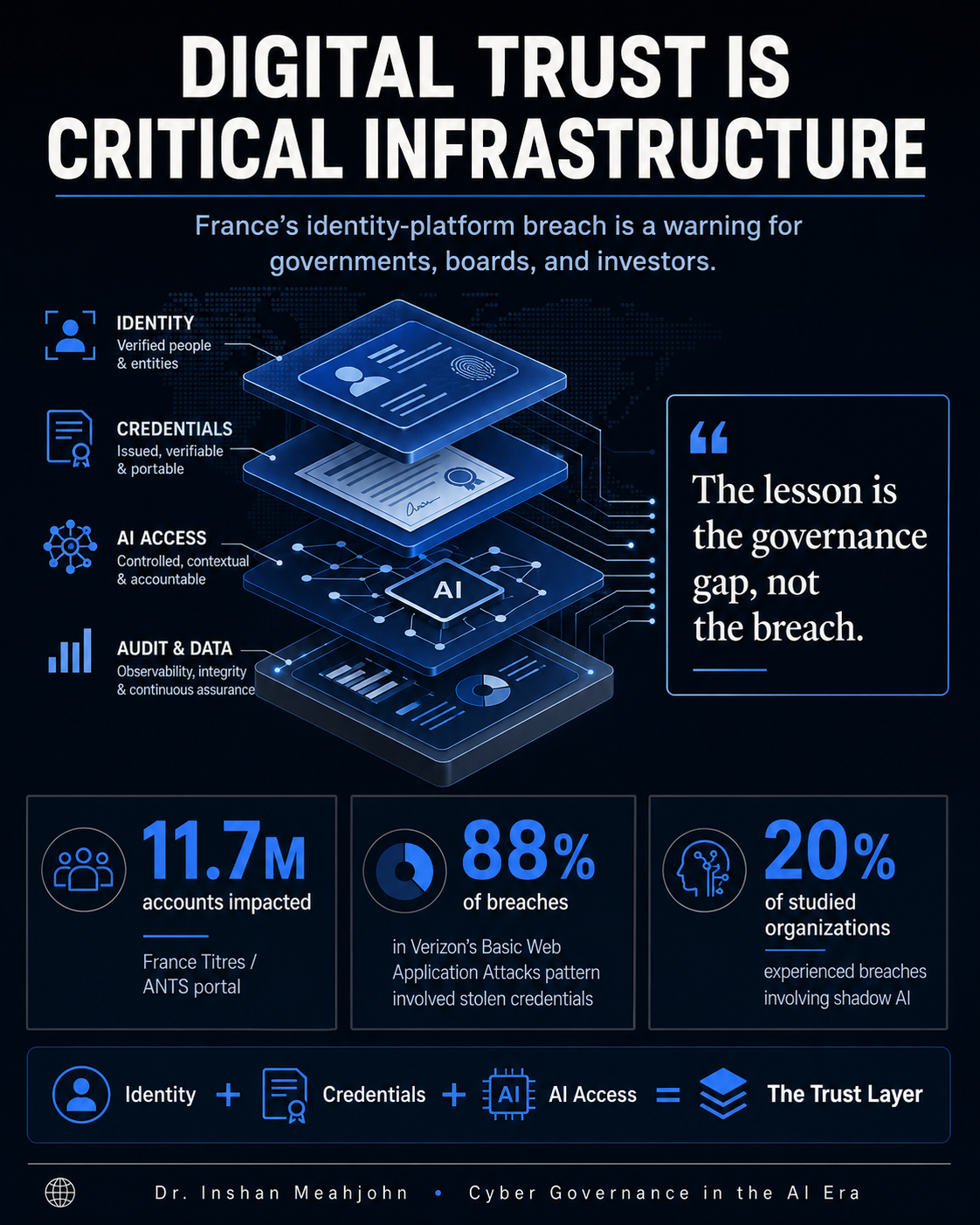
A 15-year-old extracted 11.7 million account records from the platform that issues France's ID cards, driving licences, and passports. The lesson is not the breach. It is the governance gap that made the breach possible.
Cybersecurity governance and AI governance are converging into a single trust-architecture function. Boards that have not named it yet will name it in the next incident.
What happened
On April 15, ANTS, the French agency operating under the Ministry of the Interior that issues national ID cards, driving licences, passports, and immigration documents, detected a compromise of its public portal. The agency confirmed 11.7 million accounts impacted. A threat actor using the alias "breach3d" offered up to 19 million records for sale on cybercrime forums. CNIL was notified. ANSSI was engaged. The Paris Public Prosecutor opened an investigation. On April 25, French police detained a 15-year-old.
That last sentence is the headline. A national identity platform, sitting under the Ministry of the Interior, in one of Europe's most cyber-mature jurisdictions, yielded to a teenager.
The incident does not show that France is unprepared. It shows that the threat model for national identity infrastructure has been calibrated for the wrong adversary class. A platform robust against nation-state actors but soft against a determined teenager has an architecture problem, not a capability problem.
The position this piece argues
Cybersecurity governance and AI governance are converging into a single trust-architecture function.
The technical surface, identity, credentials, access, audit, is the same for both. The accountability surface, board, regulator, public, is the same for both. The two functions cannot continue to be governed by different executives, reporting through different lines, using different vocabularies.
In the next decade, the institutions that survive their first serious AI-and-identity incident will be the ones that put the trust architecture under one accountable executive, with statutory designation, with independent assurance, and with a board reporting line that does not pass through the operating ministry or the operating CIO.
The France incident is not a cyber failure. It is a trust-architecture failure. That distinction is the argument.
Why the convergence is happening now
Three forces met in 2026.
The first is identity becoming a named target. The ANTS incident sits in a sequence that includes Aadhaar litigation in India, Jamaica's NIDS withdrawal in 2019, the OPM breach in the United States in 2015, and the rolling exposure of national identity platforms across multiple OECD jurisdictions. National identity is a top-tier target now. It will not stop being one.
The second is agentic AI moving inside the trust perimeter. Citi's launch of its Arc platform, an internal environment for governed AI agents inside a Tier-1 bank, is one of the cleanest signals to date that serious institutions are committing to AI inside the access-control model, not outside it. That commitment forces the question of who owns the audit trail when an AI agent, not a human, takes the action
The third is the visibility of the governance gap. NIS2 is in force in the EU. CISA's strategic plan is operative in the United States. The UK NCSC has issued identity-platform guidance. The Australian SOCI Act has been amended. Every serious jurisdiction has written critical-infrastructure obligations into law. Most of those obligations stop short of explicitly naming digital identity. The next round will not.
The World Economic Forum's 2026 Global Cybersecurity Outlook documents the underlying environment: accelerating AI adoption, geopolitical fragmentation, supply-chain complexity, widening capability gaps Verizon's 2026 DBIR reports that approximately 88% of breaches in its Basic Web Application Attacks pattern involved stolen credentials. IBM's 2025 Cost of a Data Breach Report records that 20% of studied organisations experienced breaches involving shadow AI, with high-shadow-AI environments incurring an additional average breach cost of USD 670,000.
These are not separate stories. They are one story about a trust architecture under pressure from credential abuse, AI proliferation, and regulatory catch-up at the same time.
Small states, structural advantage
Small island developing states and emerging economies are usually told to move faster. Adopt cloud. Modernise records. Deploy digital identity. Reduce friction. Most of that advice is correct.
What is missing is the structural argument. Small states have lower institutional density and shorter decision cycles than legacy jurisdictions. They can adopt federated and verifiable-credential architectures without legacy-migration cost. The ones that move now can build trust governance into the architecture from the first deployment, not bolted on after the first breach.
Estonia did this in the early 2000s with X-Road. The architecture was designed around verifiable consent, audit, and decentralisation, before "trust layer" was a term of art. Jamaica's NIDS programme is the counter-example: speed without consent architecture produced constitutional challenge and withdrawal in 2019. India's Aadhaar sits between the two, scaled with one architecture and contested with another.
The Caribbean Telecommunications Union's twenty-nation footprint is a place where the next generation of small-state trust architecture could plausibly be set, before the OECD draws the boundary first. The opportunity is not to keep up. The opportunity is to lead on a question the larger jurisdictions are still arguing about.
The board test
A national identity platform, or any private-sector equivalent, meets the critical-infrastructure standard if and only if five conditions hold.
First, it is statutorily designated as critical infrastructure with an associated regulatory regime.
Second, it is subject to independent annual assurance, and the assurance opinion is published.
Third, its CISO has a reporting line outside the operating ministry, the operating CIO, or the operating business unit.
Fourth, its incident protocol is exercised against both a nation-state-grade scenario and a script-kiddie-grade scenario, annually.
Fifth, breach notification is a regulated obligation with a defined window, not a goodwill gesture.
The same five-criterion test applies to banks, insurers, telecommunications providers, healthcare networks, energy operators, and universities holding equivalent volumes of identity, credential, or biometric data. The criteria do not change with the operator. They change with the asset.
If the institution cannot meet four of the five today, the institution is digitising faster than it is governing trust. That is the diagnostic.
The investor view
The investable space here is not the next firewall.
It is the platforms, services, and governance models that operate in the trust layer itself: identity, credentials, access, AI governance, cyber resilience, and the institutional capacity to maintain confidence under pressure. That space is moving from "technical product category" to "critical-infrastructure category" inside this market cycle.
Two indicators tell you when a category has crossed that line. The first is when the buyer changes from CIO to board. The second is when the regulator starts naming individual product classes. Both are happening in identity and AI governance now.
Closing
The lesson from France is not that digital identity is dangerous. The lesson is that identity, credentials, and AI access are now critical infrastructure, and the institutions that govern them as such will be the ones that retain public trust through the next incident. The institutions that do not will discover the cost of that distinction the hard way.
This piece is one author's reading of where cybersecurity and AI governance are going. The convergence claim is testable. If, in three years, AI-incident attribution has not migrated into the same governance forums as cyber-incident attribution, the claim is wrong.
The question I would put to boards, regulators, and investors is this. If a 15-year-old can extract 11.7 million national-identity records from a Ministry-of-Interior platform, the question is no longer whether your trust architecture can hold against a nation-state actor. The question is whether it can hold against a curious teenager with time, motivation, and a Discord server.
What does your answer look like in writing?
Dr. Inshan Meahjohn is Founder and CEO of DAG (Digital Alliance Global Group), a global cybersecurity and digital transformation platform operating across Caribbean, Estonian, and global markets under the operating posture Protect and Transform. He holds a PhD in Entrepreneurship from the University of Trinidad and Tobago and previously served as CEO of iGovTT, Trinidad and Tobago's national ICT agency.
Sources
- TechCrunch — France confirms data breach at government agency that manages citizens' IDs
- Cybernews — ANTS Hack: 19 million records exposed
- The Register — French prosecutors link 15-year-old to gov mega-breach
- Connexion France — ANTS data leak: up to 12 million people affected
- Help Net Security — Cyberattack on French government agency triggers phishing alert
- WEF — Global Cybersecurity Outlook 2026
- Verizon — 2026 Data Breach Investigations Report
- Axios — Citi moves into agentic AI